As your partner, we work with you to develop intralogistics solutions with effective safety concepts.
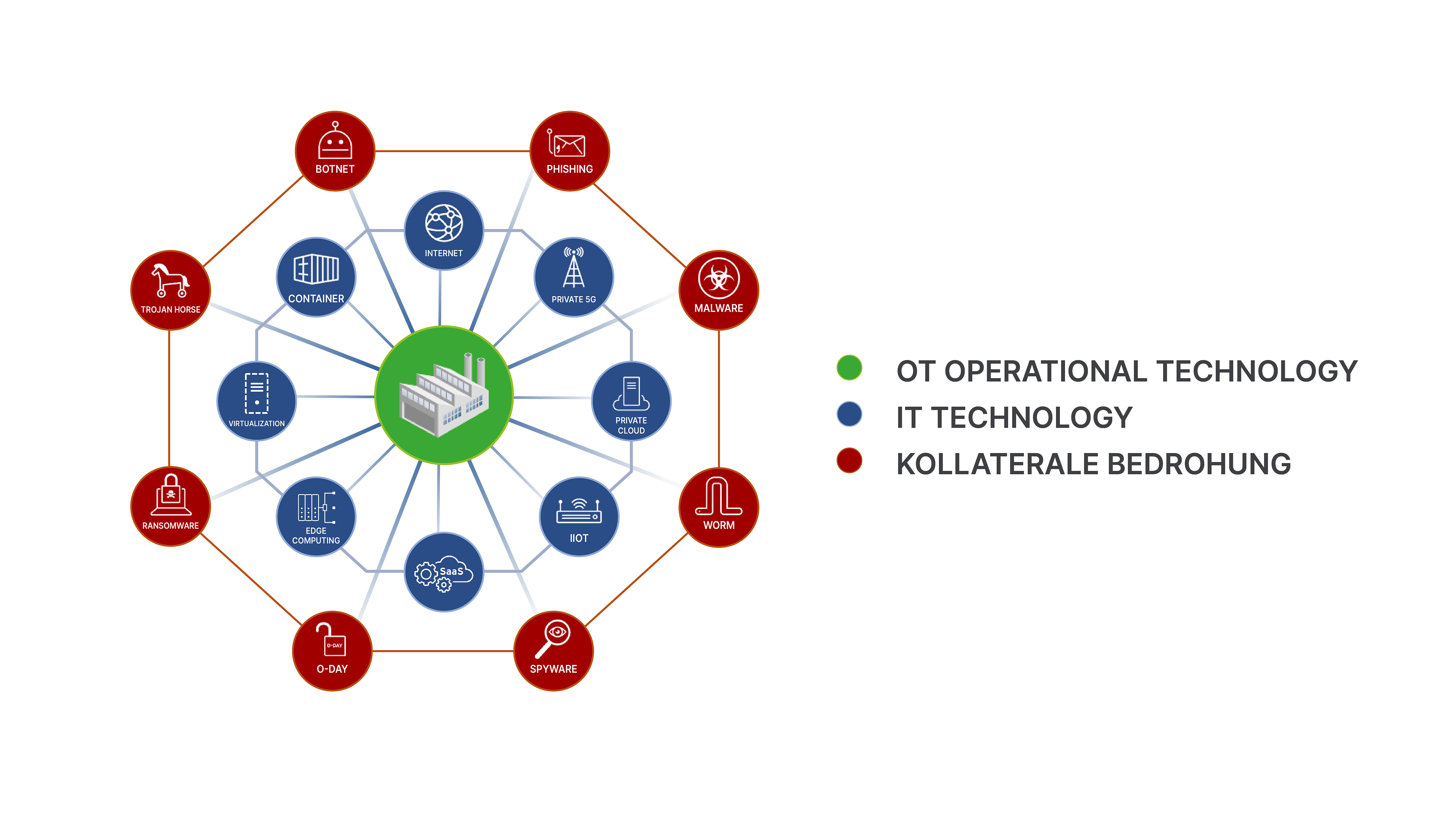
Industry 4.0 - the digital networking of the virtual and physical world - holds enormous potential. Warehouse solutions and devices can now also be raised to a completely new level of performance. Next-generation automation.
However, as industrial systems and controls (OT) become more and more connected to corporate IT, the risks of cyber attacks are also growing. OT networks and the merging with digital operating environments can open up unprecedented gateways for hackers who previously had no access to your systems.
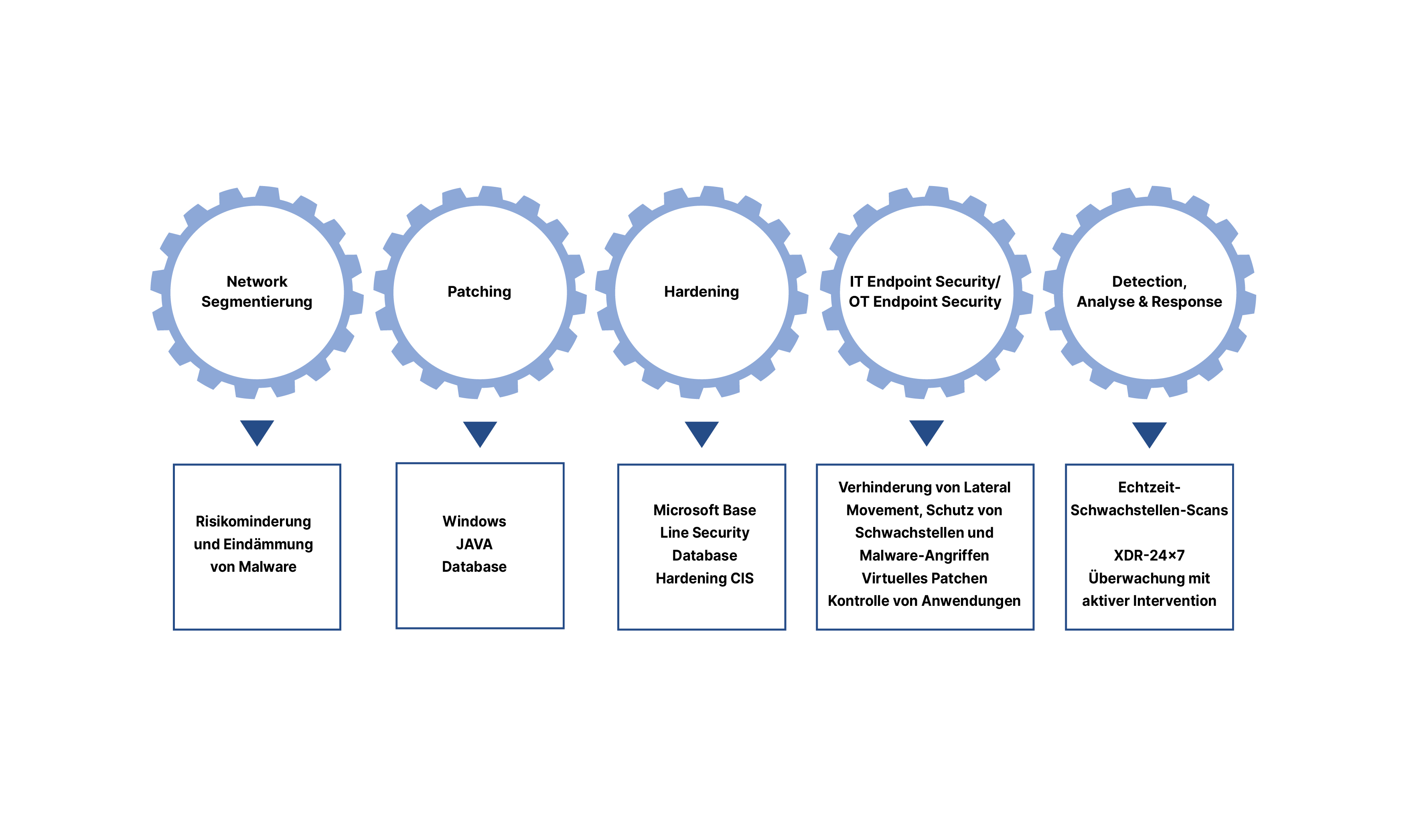
With over 40 years of experience in intralogistics and software development, we counter these threats with effective security measures that we are constantly developing further. We are guided by our five-stage package of security measures to minimize the various threats.
Our software solutions are based on holistic security management, which we develop hand in hand with a certified security partner and you.
Our solution includes the following recommendations: Network segmentation, patching, hardening, IT endpoint security / OT endpoint security as well as XDR detection and response or proactively through additional vulnerability scanners.